Featured Articles
-
How Architecture Supports Regulatory Confidence Without Slowing Delivery
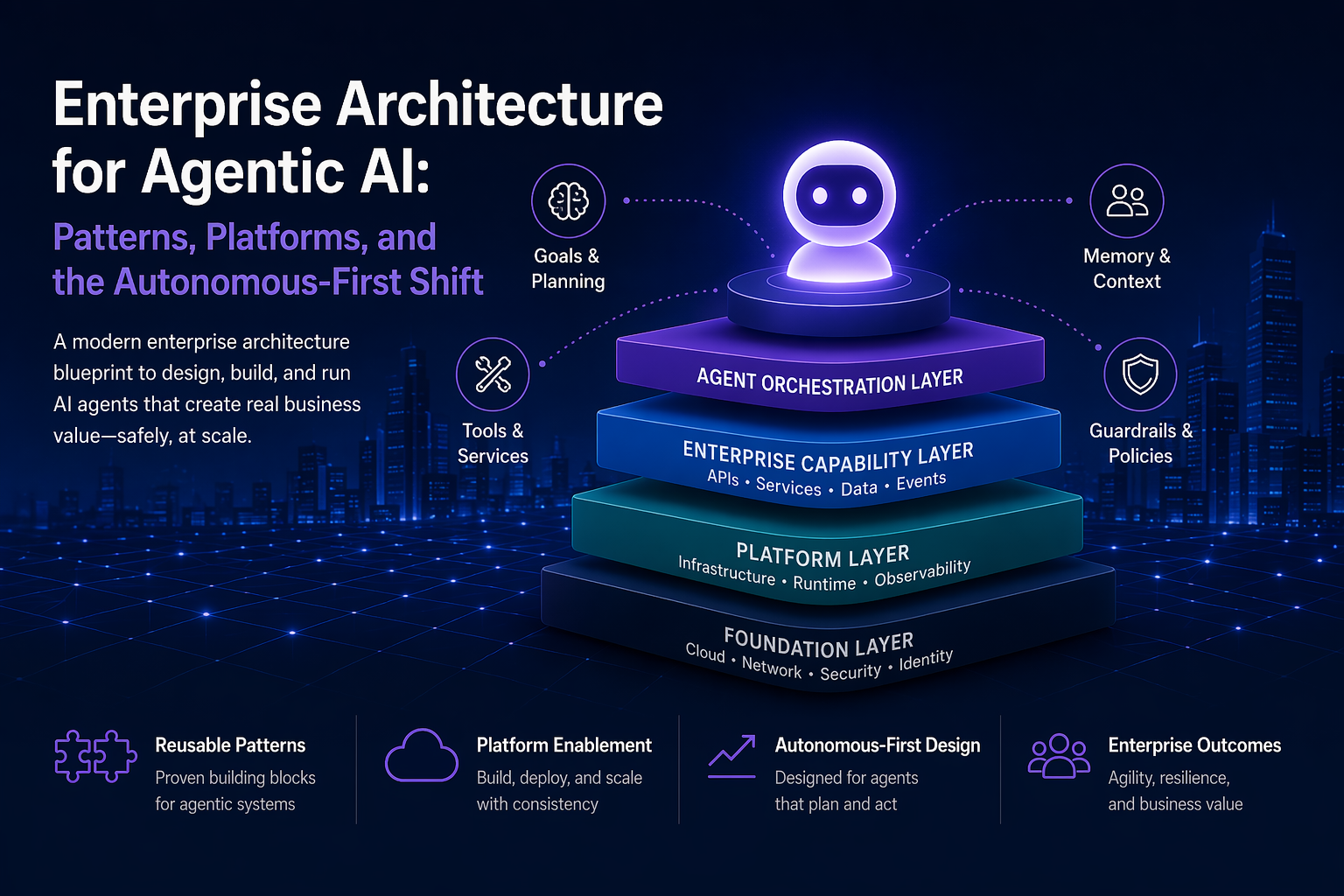
In regulated industries, organisations must balance rapid transformation with stringent regulatory assurance. Effective Enterprise Architecture fosters regulatory confidence without hindering progress. By embedding assurance early in processes and treating it as a design principle, firms enhance decision-making, visibility of risks and responsiveness to scrutiny, ultimately enabling resilient growth and innovation.