 Everyone who uses a computer or mobile creates their own digital exhaust in the form of data that we leave behind and spew out of our devices – from location data to social media posts and videos. Other things we own such as cars and houses are also generating data from SatNavs to Smart Meters.
Everyone who uses a computer or mobile creates their own digital exhaust in the form of data that we leave behind and spew out of our devices – from location data to social media posts and videos. Other things we own such as cars and houses are also generating data from SatNavs to Smart Meters.
If we could measure individual volume of data and information against todays climate change measures and visualise it, we would probably call it an ecological disaster on a person by person scale, however we go about our daily lives creating data with and without knowing it.
To be clear creating data does have a climate effect as there are systems behind what we create and they all need power, cooling etc. However, putting any talk to the side around the ecological effects of this as there is enough said already about climate and climate change and focusing on the data itself.
At the beginning of 2020, the digital universe was estimated to consist of 44 zettabytes of data, which is 44 trillion gigabytes and growing. That’s a lot of data!
We go about generating data without knowing or thinking until a news article catches our attention about something someone said many years ago. Recent times have seen an almost doubling of the use of the internet. This in turn increases the amount of data being created as people discover ways to help elivate lockdown with video calls to new dances on TikTok.
To put this into perspective a bit, with a trolley full of phones you can create a virtual traffic jam, but dont try that at home. This example illustrates the data being generated from a device and how others are using it, in this case to look at traffic patterns
In this increase of posts and data about people across the many different platforms available, are you stopping to think about what your posting? We go about generating data without thinking until a news article catches our attention about something someone said many years ago that has been found on a social platform somewhere.
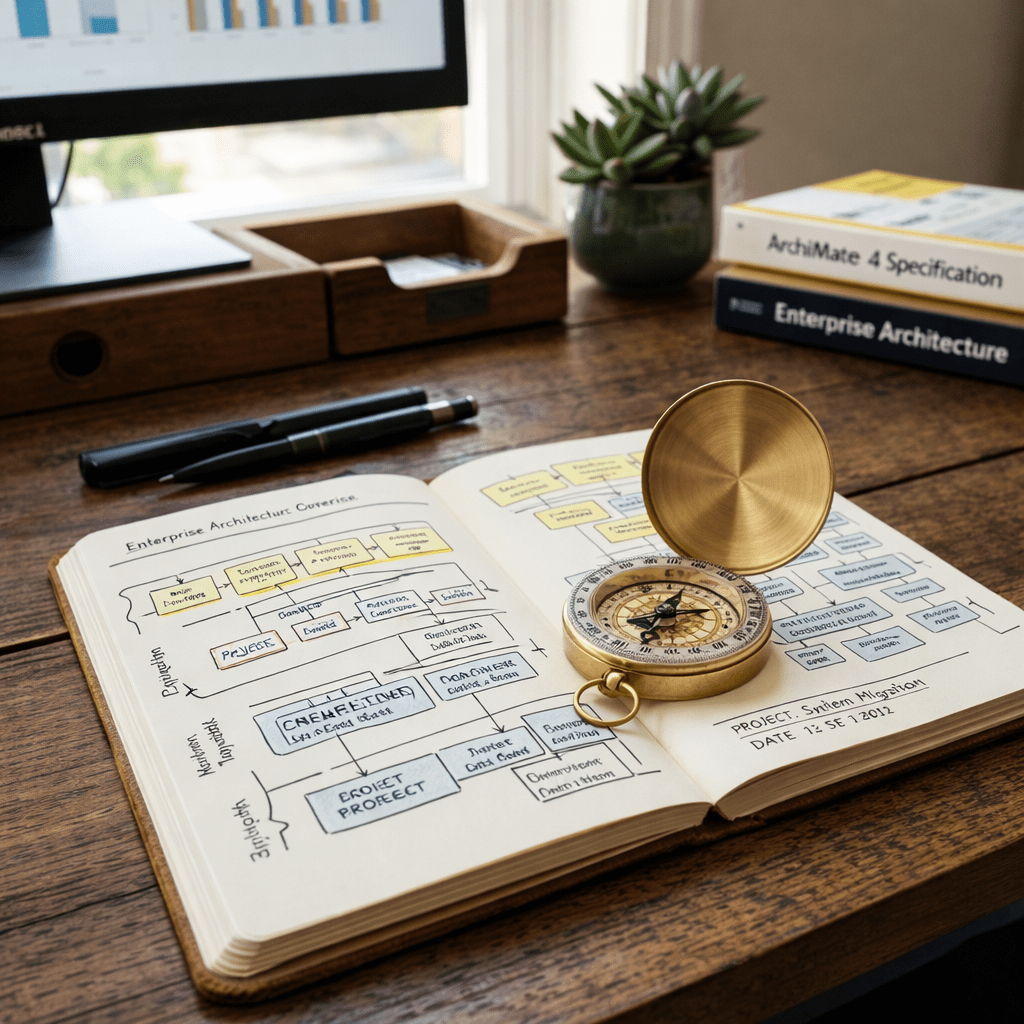
Sci-Fi moment alert! – Having watched an episode of “The Orville” by Seth MacFarlane called “Lasting Impressions” where the crew of the Orville open a Time Capsule and recreate someones life in a holodeck using just the data from a iPhone (after accessing a video on the phone where the person who’s phone it is, gives their consent for the data to be used in the future) and recreate and interact with the phones original owner. This provides the crew with a view into that persons life and what they were like.
Have you through about what would happen to your data in the future?
This concept can easily be recreated today and there are TV programs that investigate and look at people to check who they really are (Catfish the TV show). Its easy to see how people leave a trail of digital evidence and clues from what they post and are not secure on what they do or think about what they post.
Here are some good tips to help secure your online presence:
Privacy and security settings exist for a reason: Learn about and use the privacy and security settings on social networks. They are there to help you control who sees what you post and manage your online experience in a positive way.
Once posted, always posted: Protect your reputation on social networks. What you post online stays online. Think twice before posting pictures you wouldn’t want your parents or future employers to see. Recent research found that 70 percent of job recruiters rejected candidates based on information they found online.
Your online reputation can be a good thing: Recent research also found that recruiters respond to a strong, positive personal brand online. So show your smarts, thoughtfulness and mastery of the environment.
Keep personal info personal: Be cautious about how much personal information you provide on social networking sites. The more information you post, the easier it may be for a hacker or someone else to use that information to steal your identity, access your data or commit other crimes such as stalking.
Know and manage your friends: Social networks can be used for a variety of purposes. Some of the fun is creating a large pool of friends from many aspects of your life. That doesn’t mean all friends are created equal. Use tools to manage the information you share with friends in different groups or even have multiple online pages. If you’re trying to create a public persona as a blogger or expert, create an open profile or a “fan” page that encourages broad participation and limits personal information. Use your personal profile to keep your real friends (the ones you know and trust) up to date with your daily life.
Be honest if you’re uncomfortable: If a friend posts something about you that makes you uncomfortable or seems inappropriate, let them know. Likewise, stay open minded if a friend approaches you because something you’ve posted makes him or her uncomfortable. People have different tolerances for how much the world knows about them respect those differences.
Know what action to take: If someone is harassing or threatening you, remove them from your friends list, block them and report them to the site administrator.
Keep security software current: Having the latest security software, web browser and operating system is the best defense against viruses, malware and other online threats.
Own your online presence: When applicable, set the privacy and security settings on websites to your comfort level for information sharing. It’s OK to limit how and with whom you share information.
Source: https://staysafeonline.org/stay-safe-online/securing-key-accounts-devices/social-media/
Additional tips are available at this source.


Leave a comment