 Security is one of the main “IoT Standards” that a lot of groups, communities, vendors and manufacturers are currently tackling. The IoT is creating a vast amount of opportunities for sensors and devices to be created and used, but also creating a vast amount of security areas that need to be considered.
Security is one of the main “IoT Standards” that a lot of groups, communities, vendors and manufacturers are currently tackling. The IoT is creating a vast amount of opportunities for sensors and devices to be created and used, but also creating a vast amount of security areas that need to be considered.
Due to the possible combinations of sensors and uses available for IoT devices this makes having a single standard or solution impossible. Instead security will evolve in a layered approach with the ability to be interlinked within a device in order to provide the layer of security needed. As well as combining these layers it is also important that any security applied is up to date and if possible has the ability to be kept up to date with latest patches and updates.
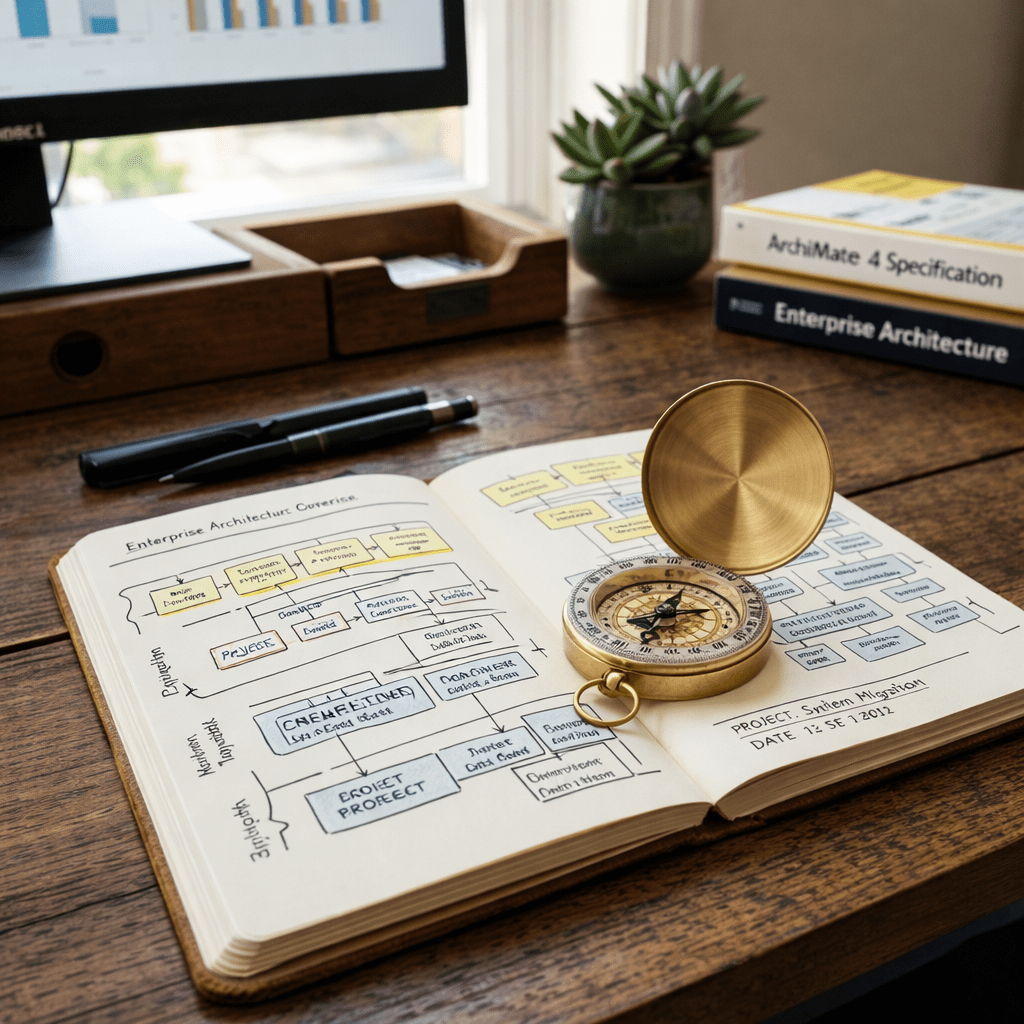
Below is an illustration of some possible layers that need to be considered when looking into designing an IoT device.
I will delve a bit deeper into each of these areas in following blog posts (Links below updated as each post is written)



Leave a reply to IoT Device Security Considerations and Security Layers – Chipset | Max Hemingway Cancel reply